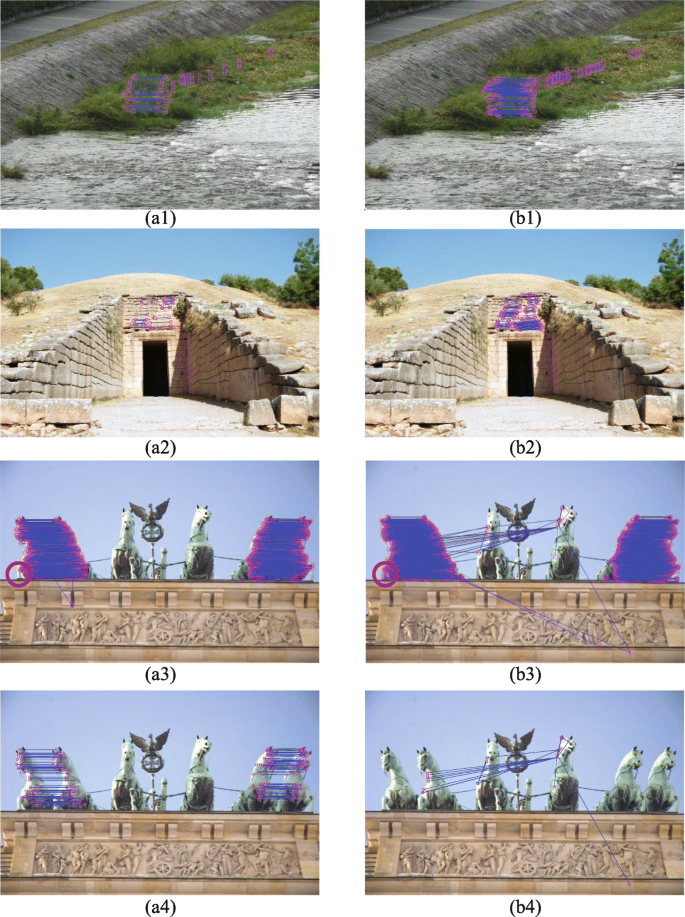
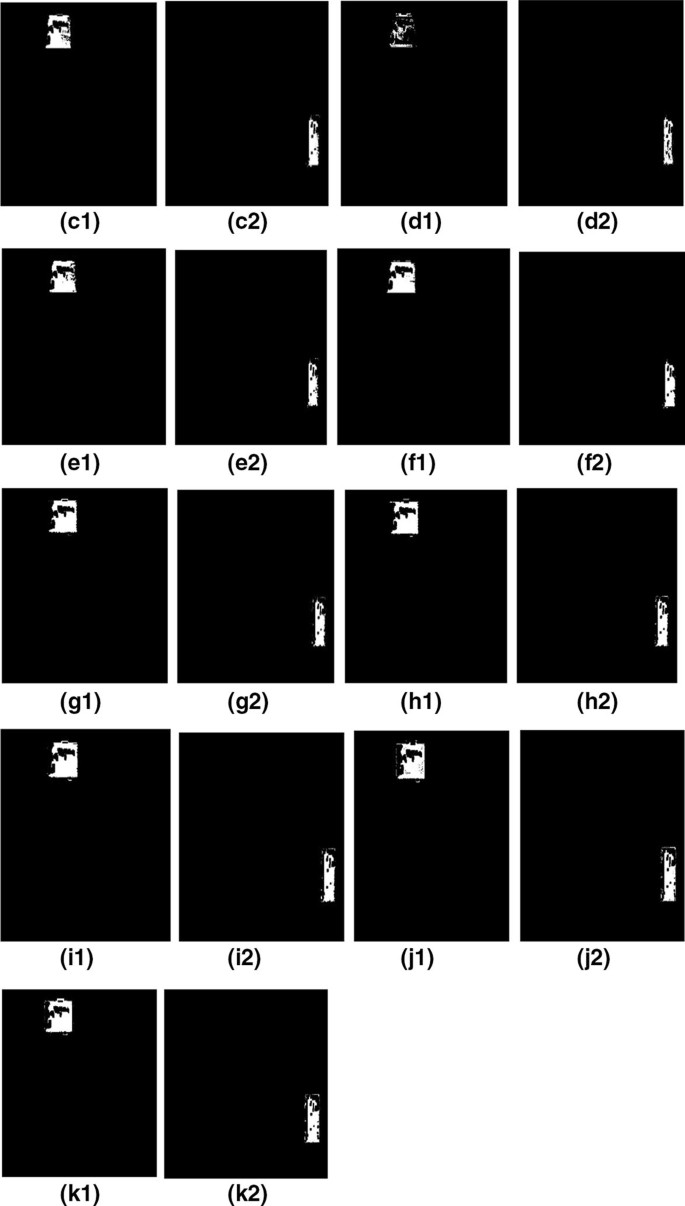
a1), {(b1)-(c1)}, (d1), (e1), and {(f1)-(g1)} shows copy-move forged
Por um escritor misterioso
Descrição

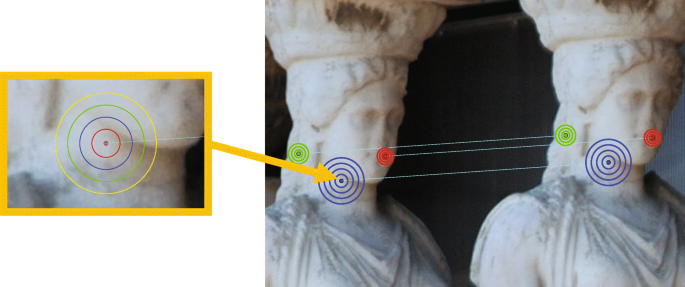
Example for copy-move forgery from [MS07] (original image left
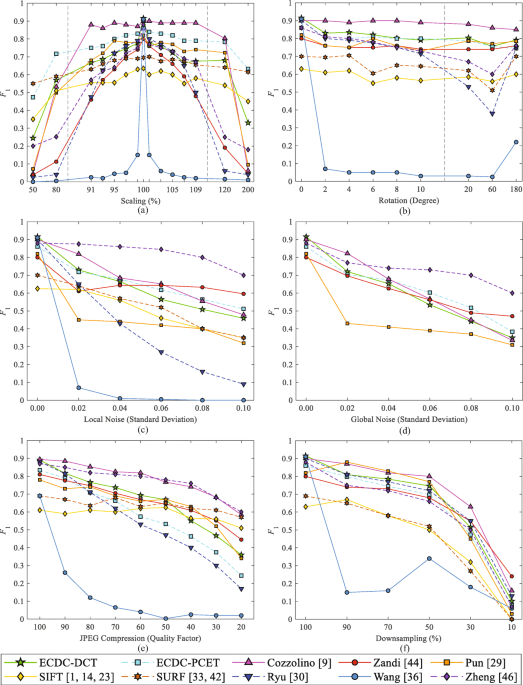
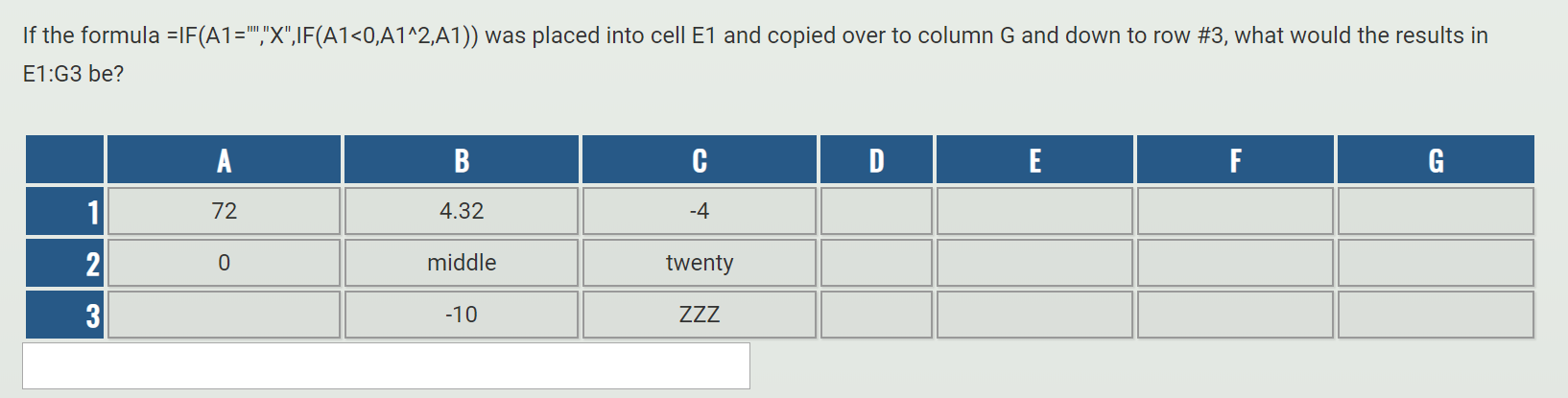
Copy-move image forgery detection based on evolving circular domains coverage
Copy-move image forgery detection based on evolving circular domains coverage

a1), (b1), (c1), (d1), (e1), and (f1) shows forged images with

a1) and (a2) shows original and copy-move forged image, respectively.
Copy-move image forgery detection based on evolving circular domains coverage

PDF] Copy-Move Forgery Detection Utilizing Local Binary Patterns

Copy-move image forgery detection based on evolving circular domains coverage
Solved If the formula =IF(A1=,X,IF(A1<0,01^2,A1)) was
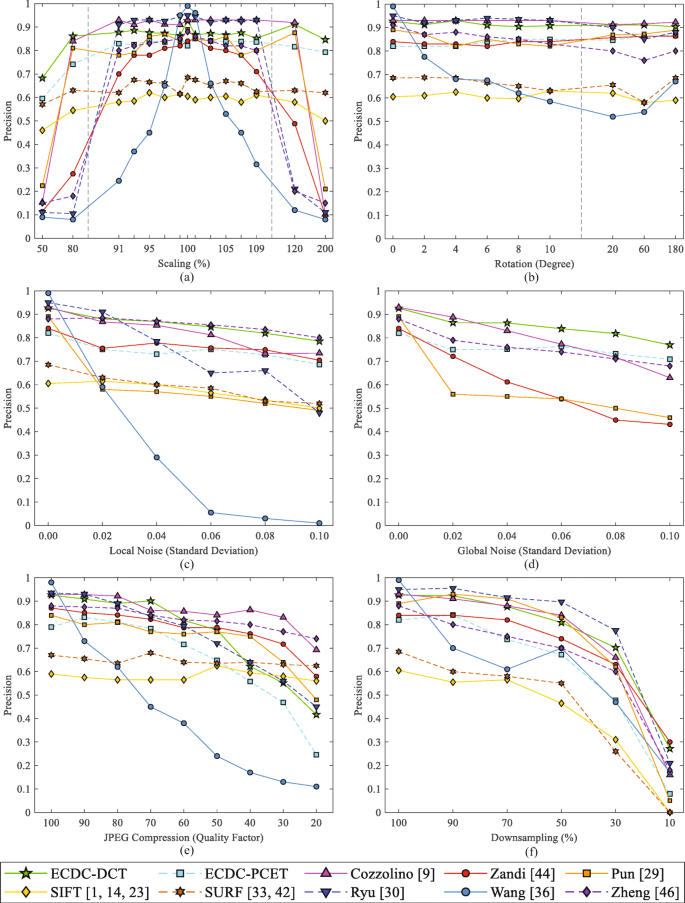
Solved Question 4. [18 marks] (a) Let E = {V1, V2, V3} and F

The first five examples for Copy-Move forgery detection: original
The first five examples for Copy-Move forgery detection: original
Copy-move image forgery detection based on evolving circular domains coverage
Copy-Move Forgery Detection Based on Discrete and SURF Transforms
de
por adulto (o preço varia de acordo com o tamanho do grupo)