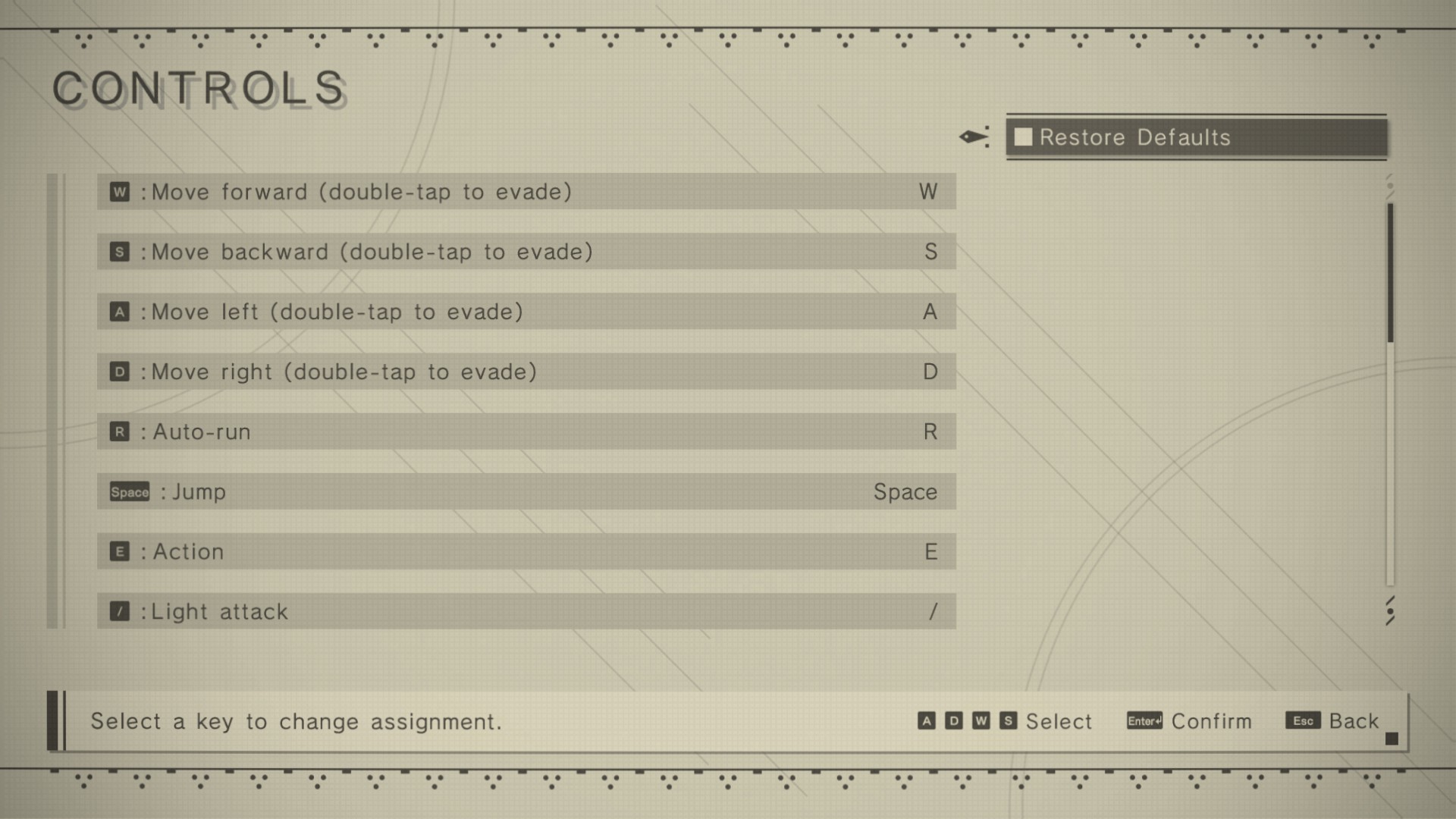
Suspicious User Controls
Por um escritor misterioso
Descrição
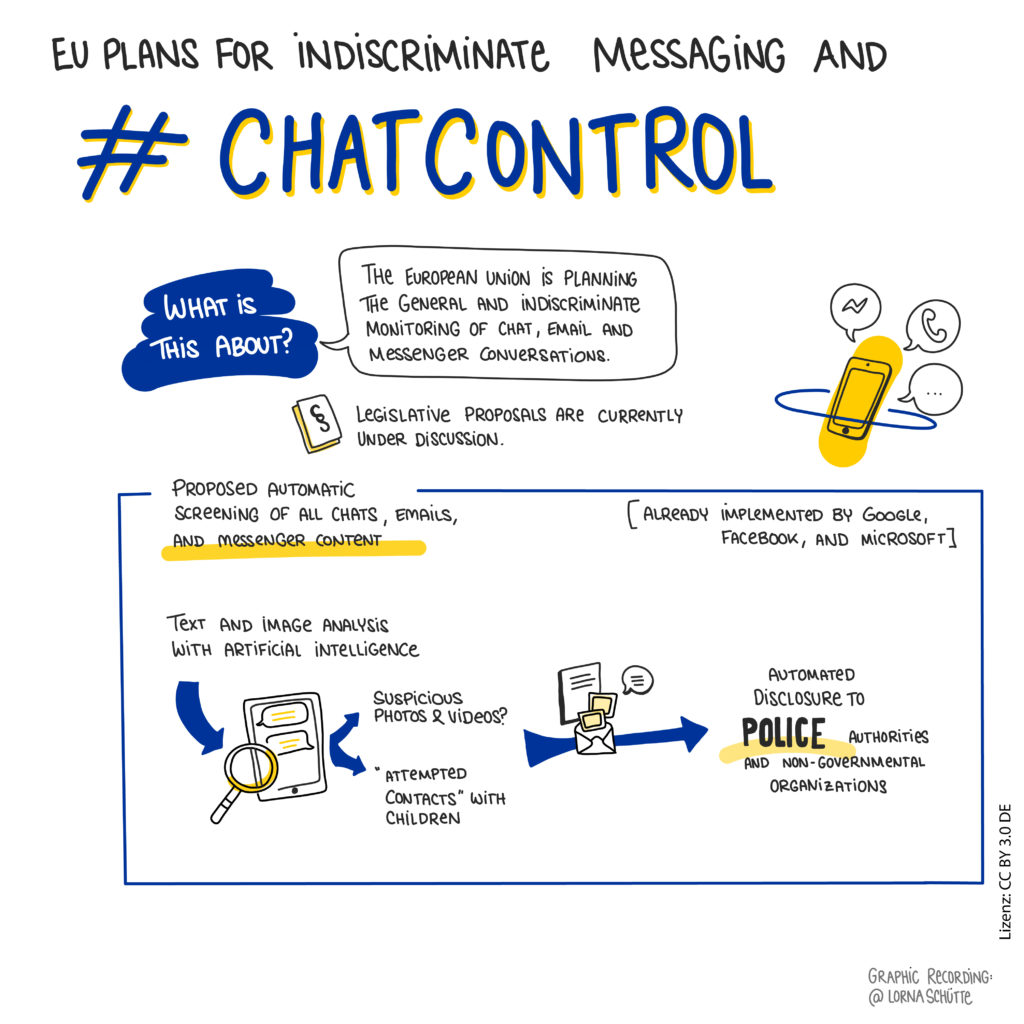
Chat Control: The EU's CSEM scanner proposal – Patrick Breyer

DETEGO de-anonymizes fraud. Fraud detection only identifies suspicious
Taking Back Control of Your SOC with Risk Based Alerting

Stronger Access Control Management - Enterprise Network Security Blog from IS Decisions
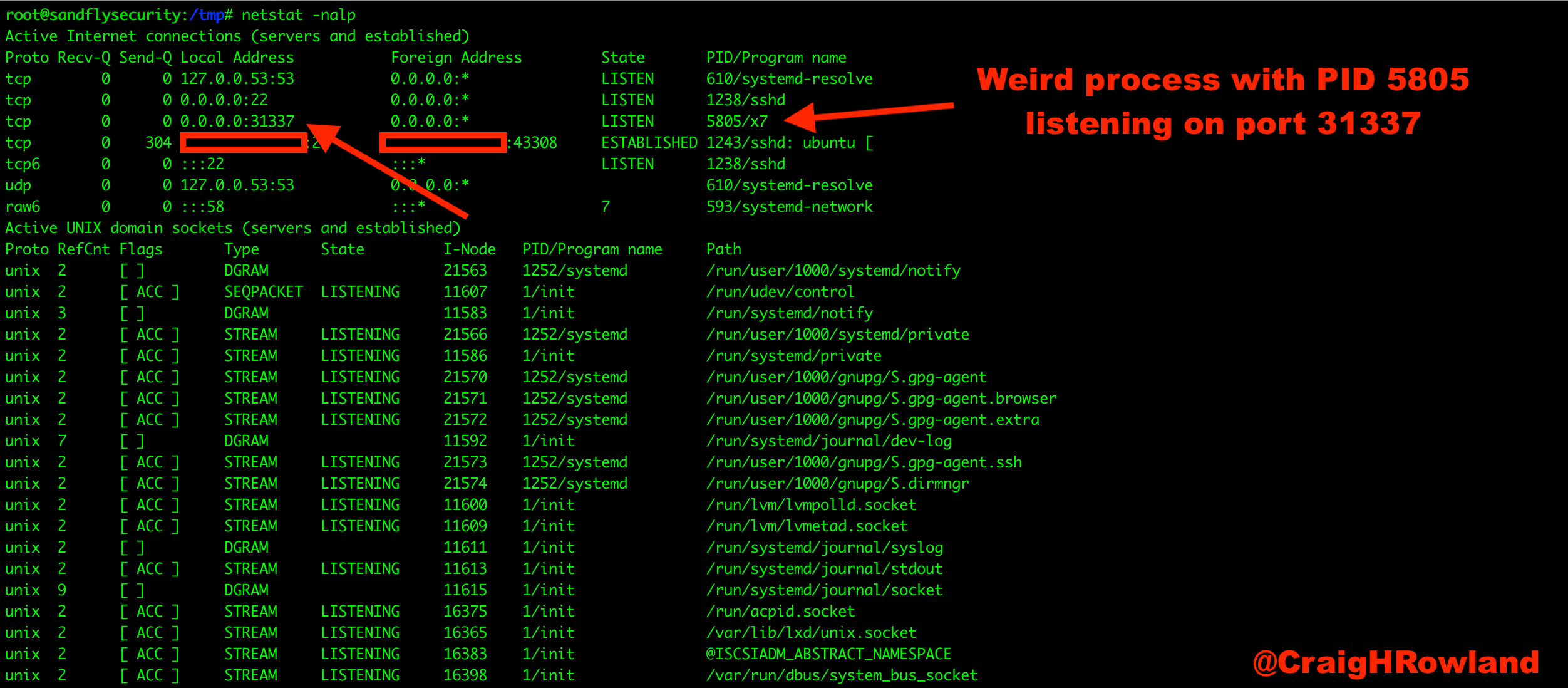
How to: Basic Linux malware process forensics for incident responders

RUMOR CONTROL: Users report suspicious text across Mobile, Baldwin counties
Hunting for Suspicious DNS Requests with Short Domain Extensions

Detect Potentially Suspicious Activity In Teams With Cloud App Security – Sam's Corner

How DevOps is accelerating innovation in 2023: Pulumi, GitOps Solutions, and more!, Periscope-Tech posted on the topic
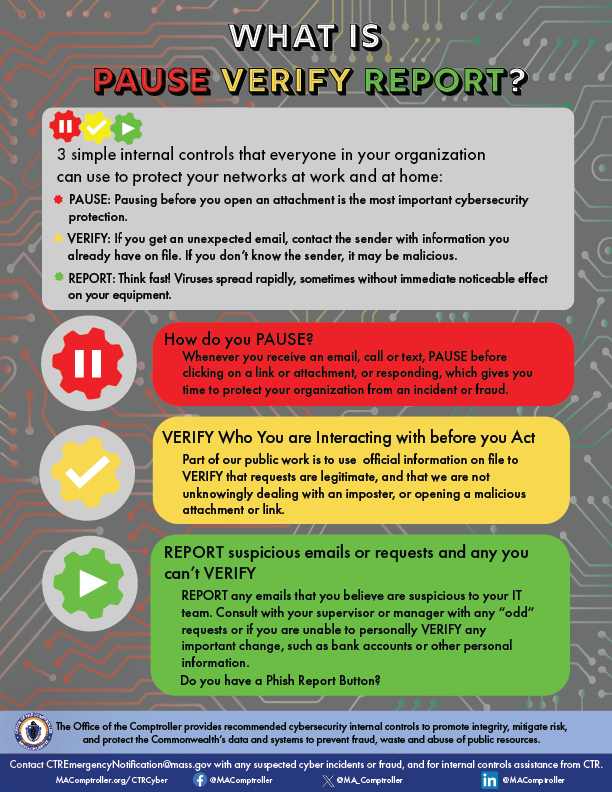
What is PAUSE VERIFY REPORT? - Office of the Comptroller
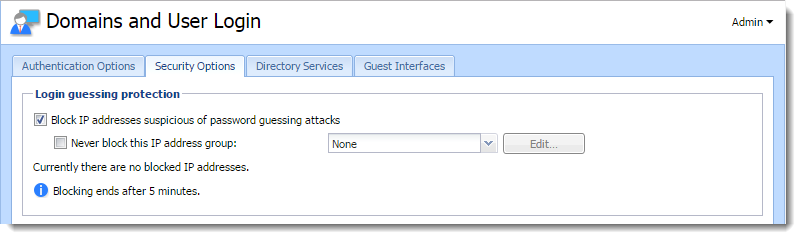
Protecting users against password guessing attacks

PDF] Suspicious-Taint-Based Access Control for Protecting OS from Network Attacks
I love lancer : r/Deltarune
de
por adulto (o preço varia de acordo com o tamanho do grupo)