Malware analysis Malicious activity
Por um escritor misterioso
Descrição
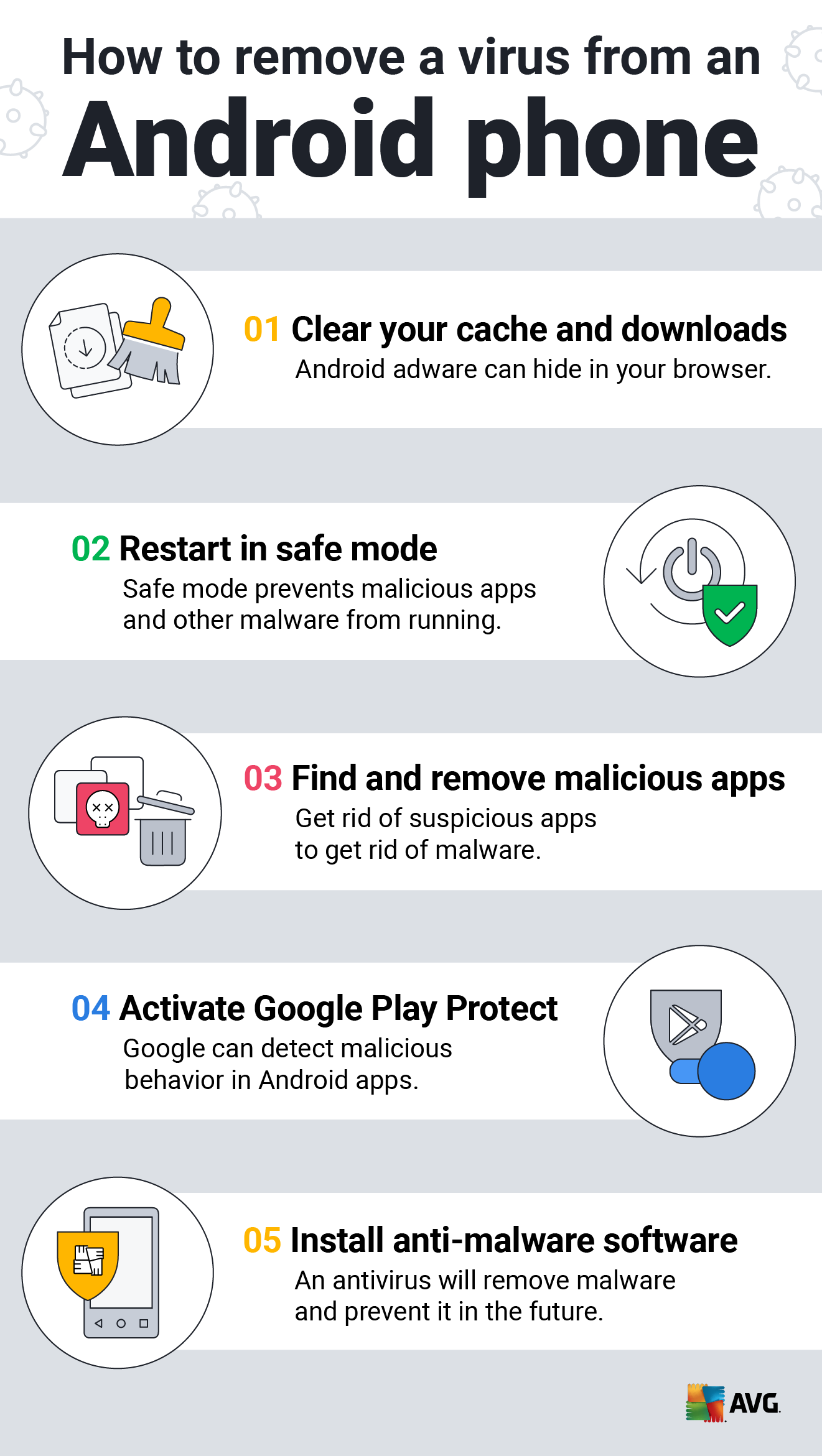
How to Clean an Android or iPhone from Viruses for Free

Dynamic malware analysis [34]

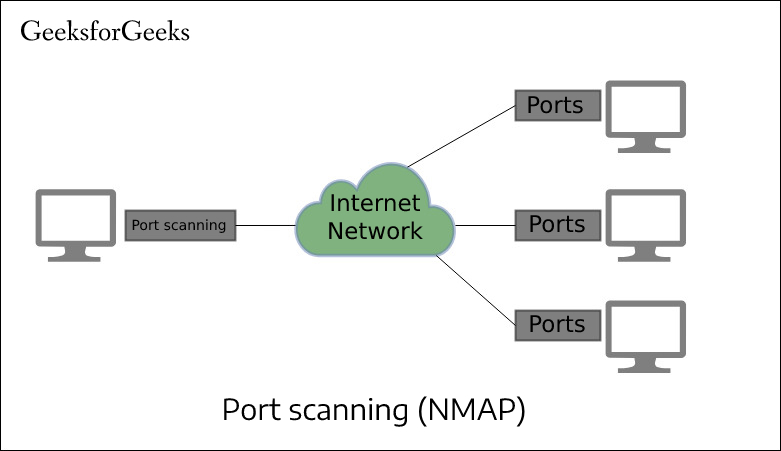
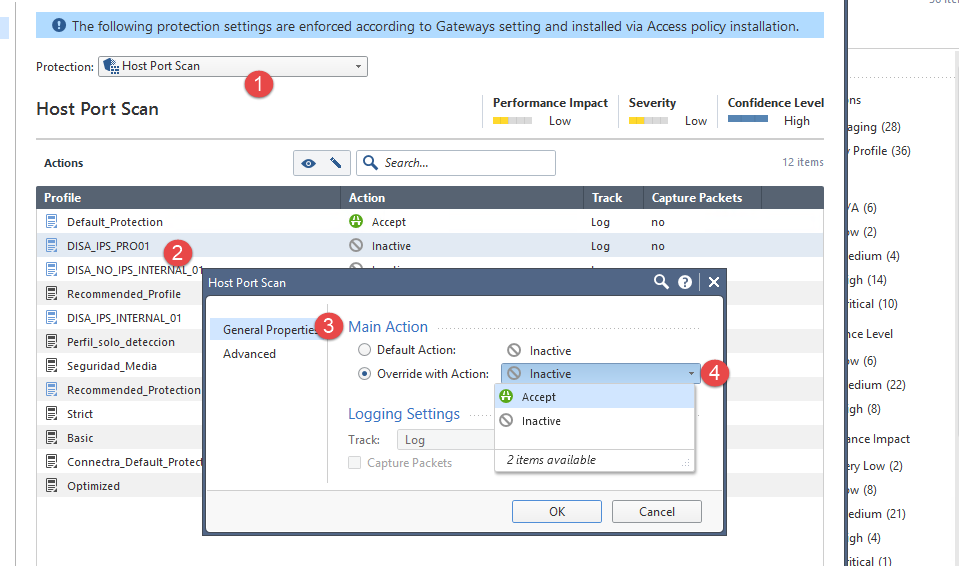
How to Analyze Malware's Network Traffic in A Sandbox

Building A Simple Malware Analysis Pipeline In The Homelab Pt - 1 · Arch Cloud Labs

Mastering Malware Analysis
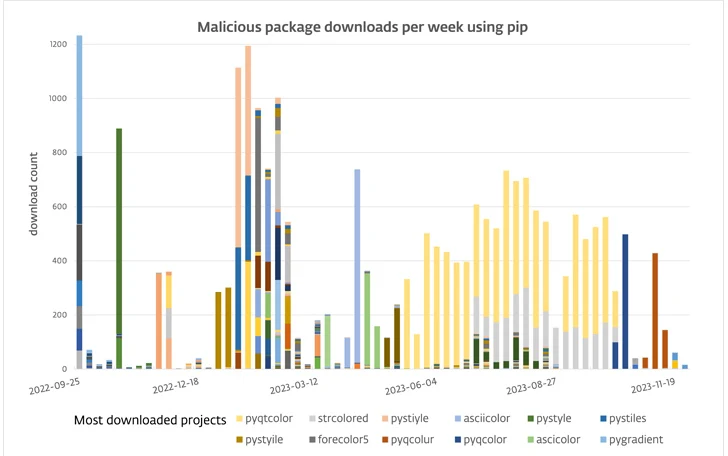
116 Malware Packages Found on PyPI Repository Infecting Windows and Linux Systems

Malware Analysis: Steps & Examples - CrowdStrike

Malware - Wikipedia

What is Malware? Definition, Types, Prevention - TechTarget
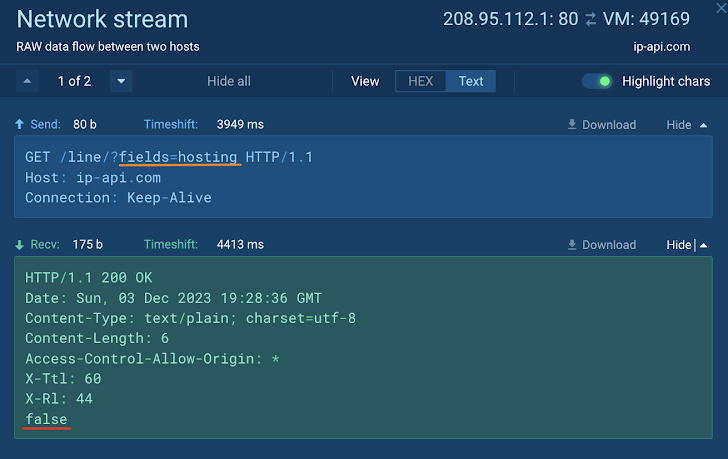
How to Analyze Malware's Network Traffic in A Sandbox

MetaDefender Cloud Advanced threat prevention and detection
de
por adulto (o preço varia de acordo com o tamanho do grupo)