Grouping Multiparty Key Generation.
Por um escritor misterioso
Descrição

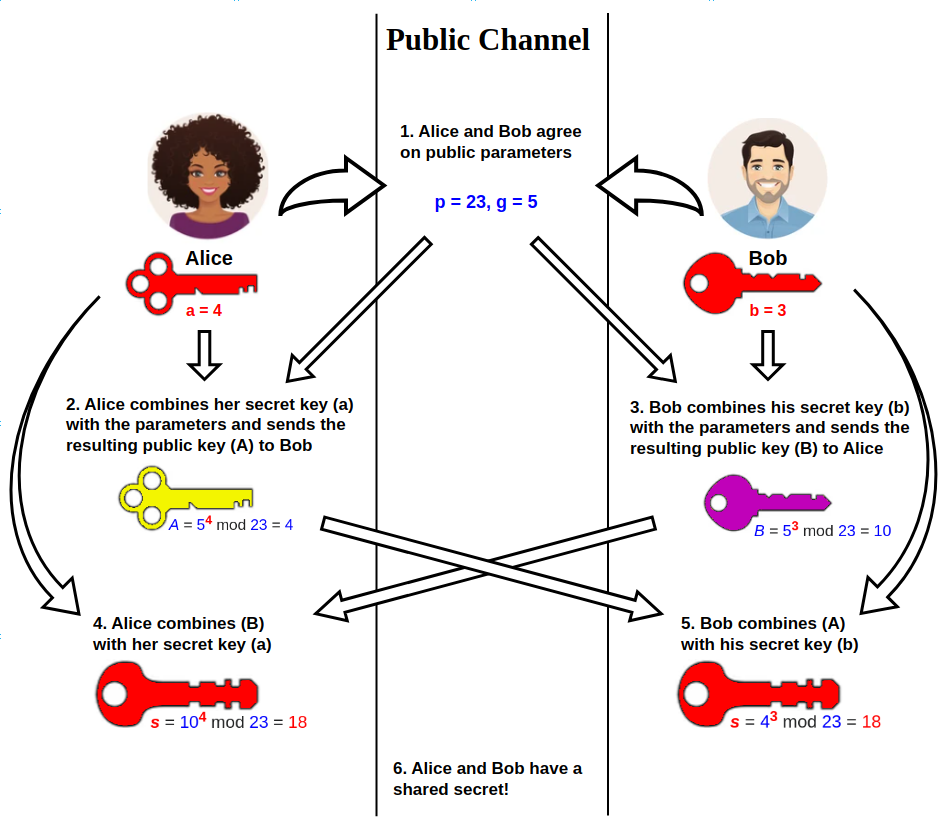
PDF] Diffie-Hellman technique: extended to multiple two-party keys and one multi-party key

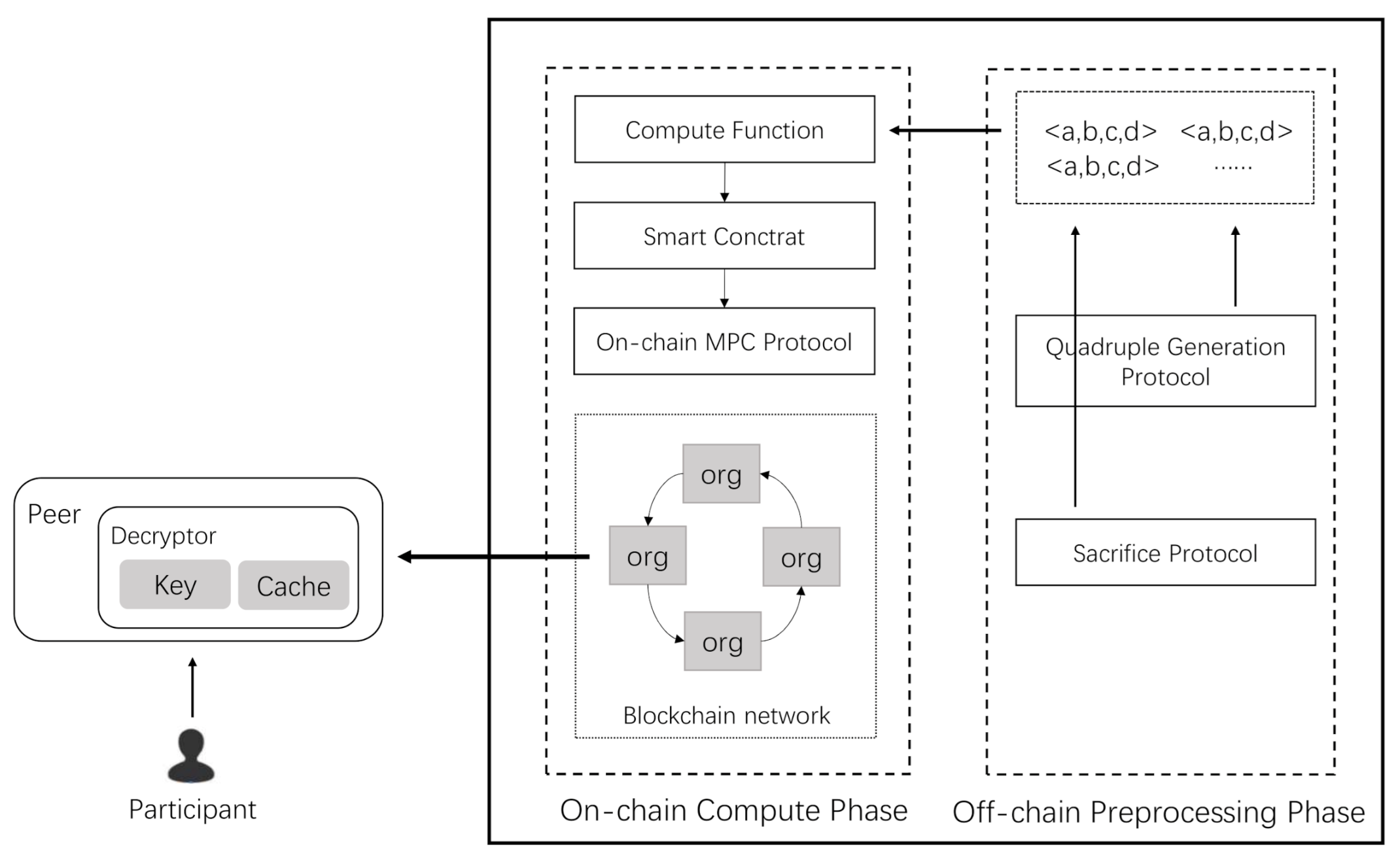
Efficient sharing of privacy-preserving sensing data on consortium blockchain via group key agreement - ScienceDirect
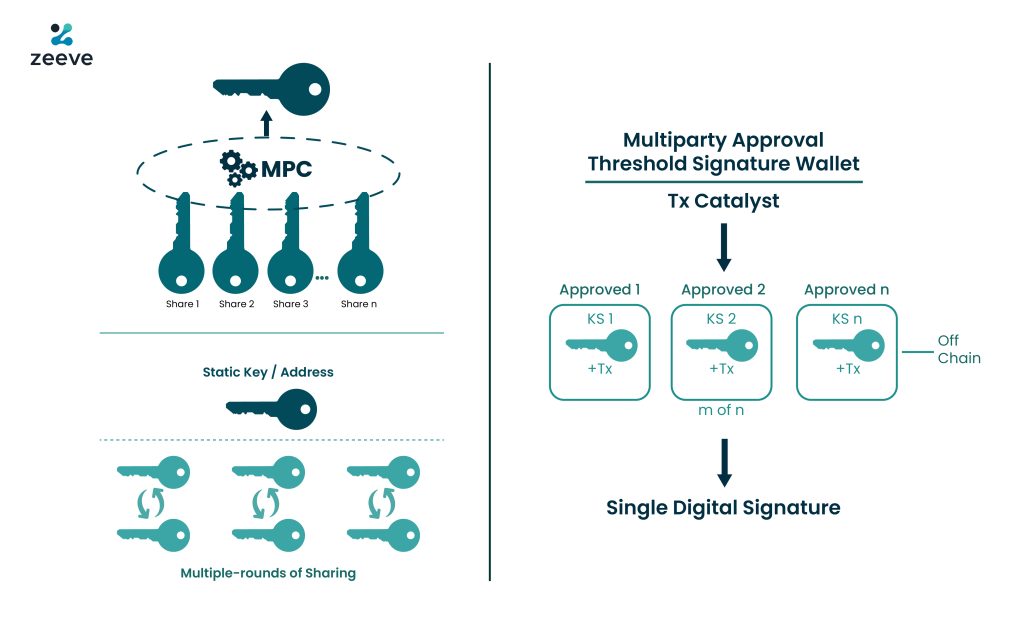
What is the Threshold signature scheme(TSS)? Multi-party Computation(MPC) simplified

Privacy preserving computing and secure multi party computation
Sensors, Free Full-Text

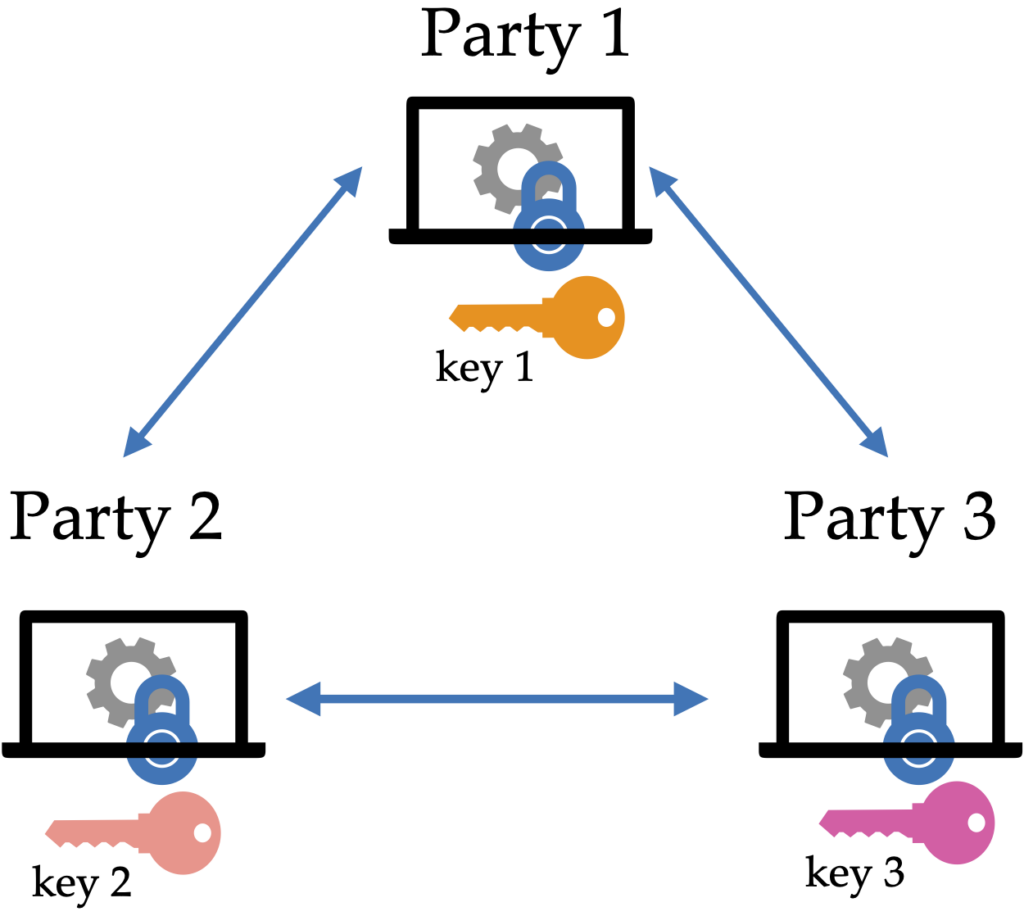
The Three Musketeers of Secure Computation: MPC, FHE and FE - COSIC

Experimental quantum conference key agreement
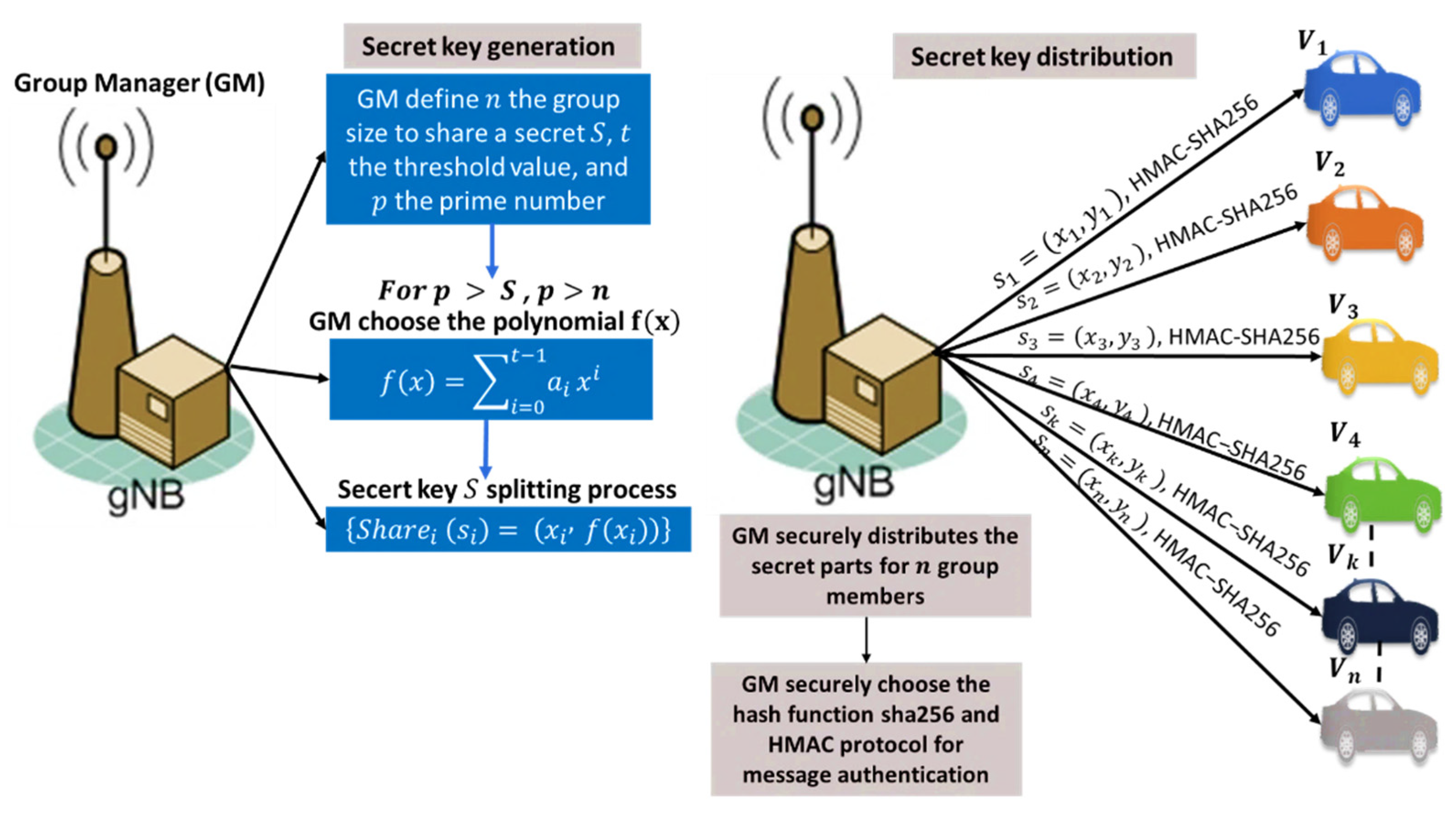
Sensors, Free Full-Text

Multi‐party key generation protocol for the identity‐based signature scheme in the IEEE P1363 standard for public key cryptography - Feng - 2020 - IET Information Security - Wiley Online Library

Secure Multi-Party Computing (sMPC) — Collaboration Without Sharing, by Mabel Oza, Coinmonks
Secure computation: Homomorphic encryption or hardware enclaves? - Opaque

Multi-party interactive cryptographic key distribution protocol over a public network based on computational ghost imaging - ScienceDirect
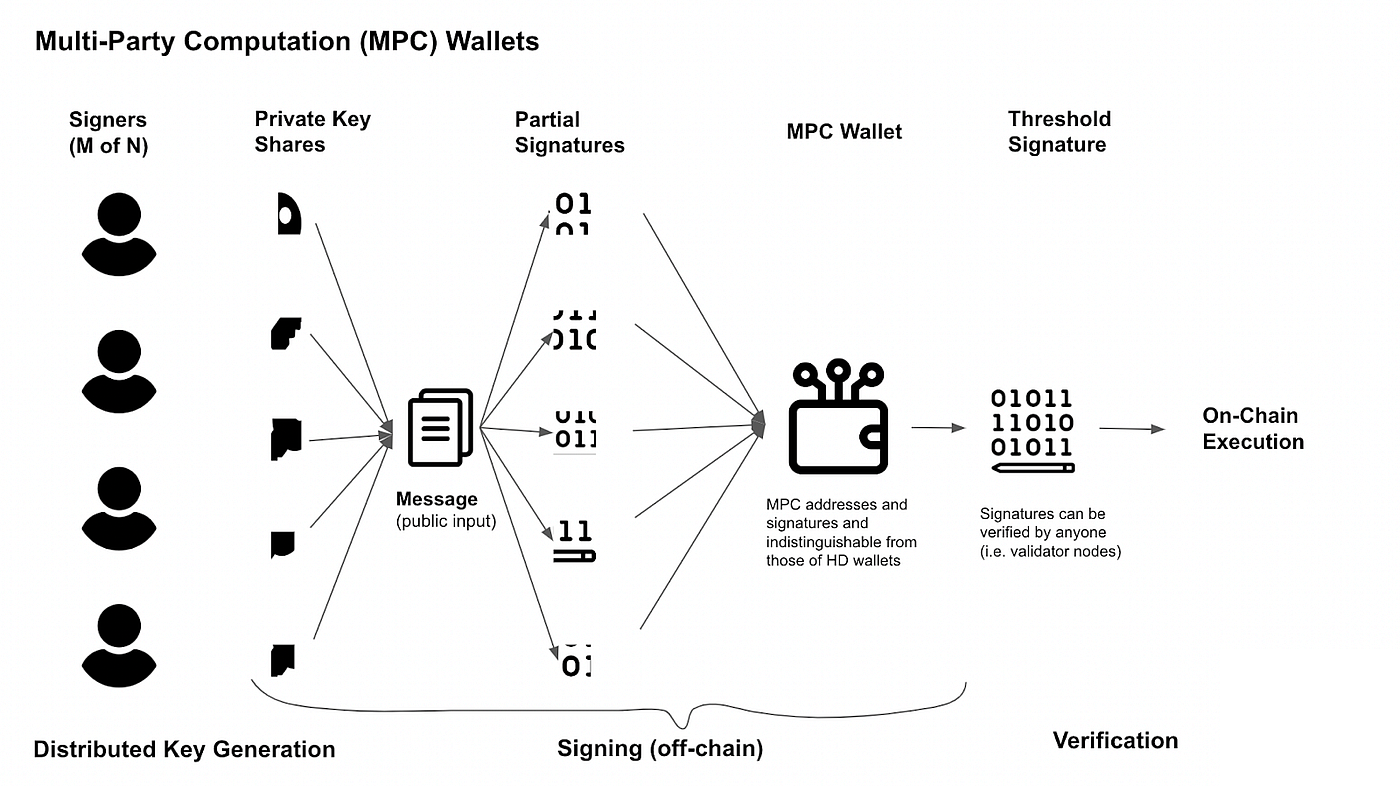
MPC vs Multi-sig — Misconceptions and Valid Arguments
de
por adulto (o preço varia de acordo com o tamanho do grupo)