Pawn Storm Abuses OAuth In Social Engineering Attacks
Por um escritor misterioso
Descrição
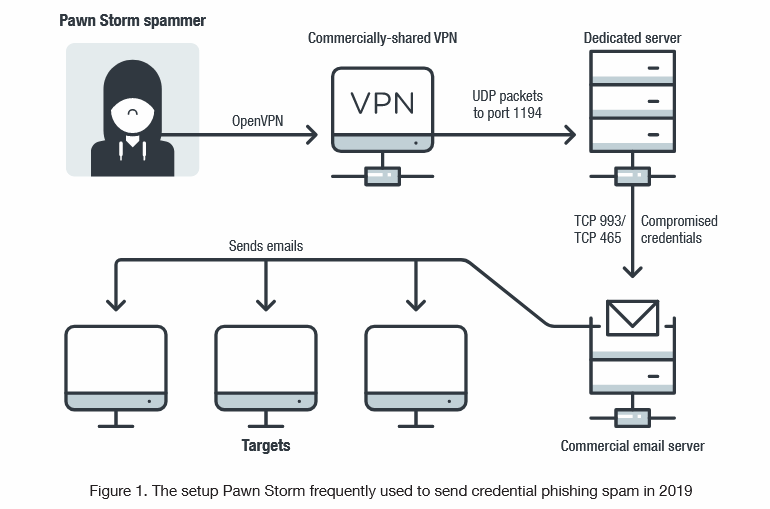
This blog post discusses how Pawn Storm abused Open Authentication (OAuth) in advanced social engineering schemes. High profile users of free webmail were targeted by campaigns between 2015 and 2016.
The real story behind the latest Pawn Storm attack and the Windows zero-day patch release

2020 Cyber Attacks Statistics – HACKMAGEDDON
Detection and Mitigation of Illicit Consent Grant Attacks in Azure AD - Thomas Naunheim
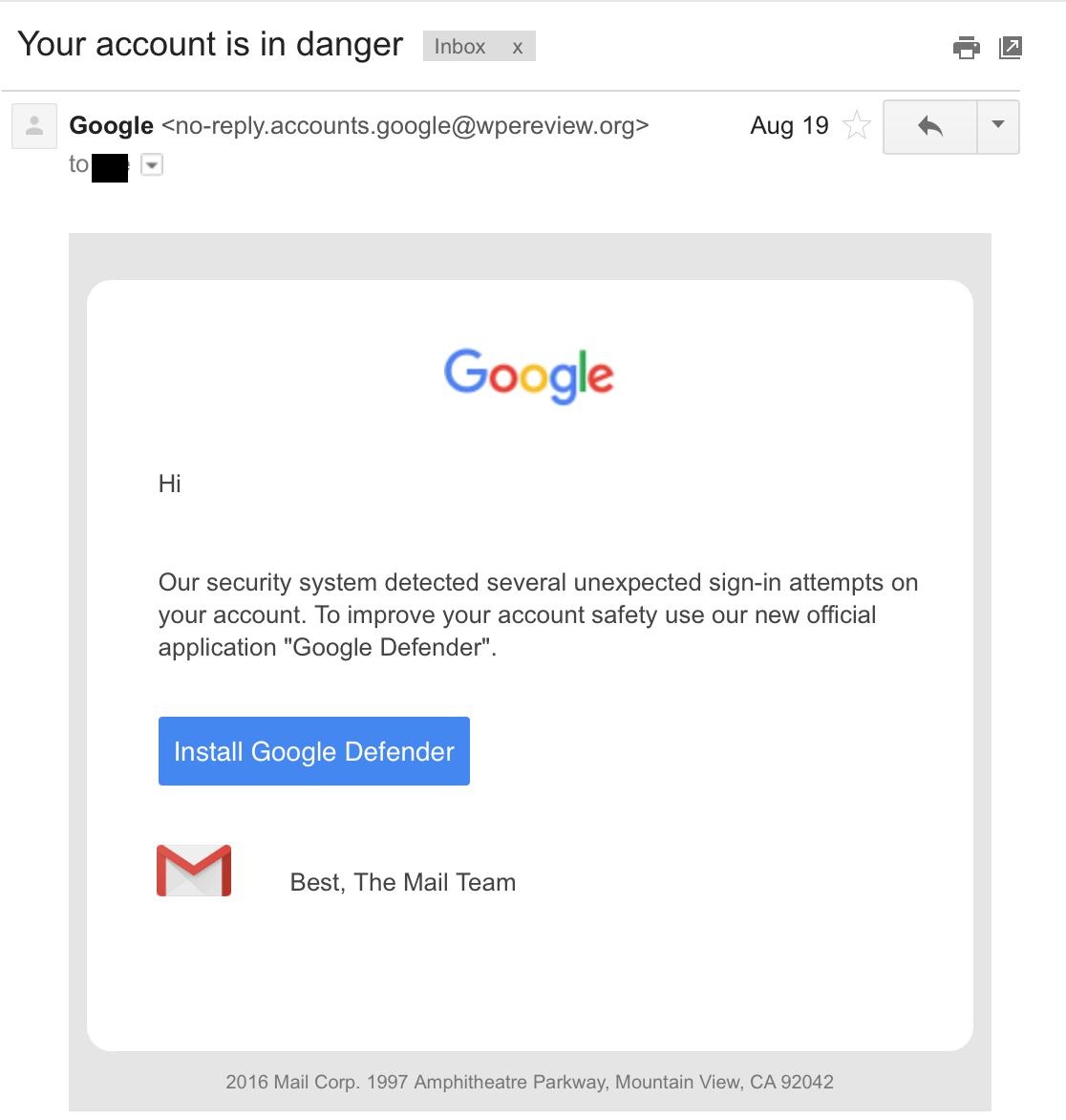
Pawn Storm Abuses OAuth In Social Engineering Attacks

Social Engineering Attacks: Definition, Examples, Prevention

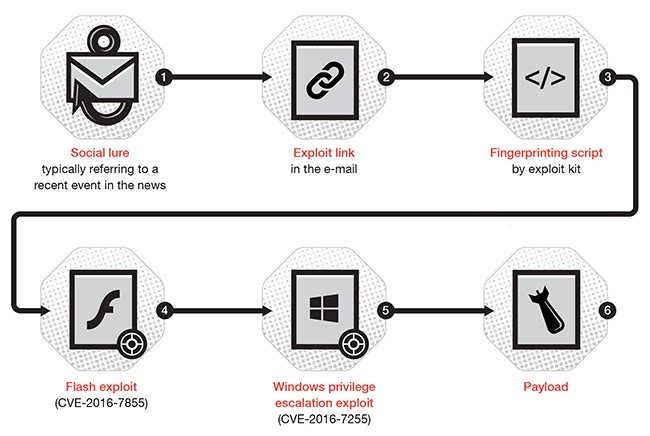
Pawn Storm Mishandles Open Authentication in Advanced Social Engineering Attacks
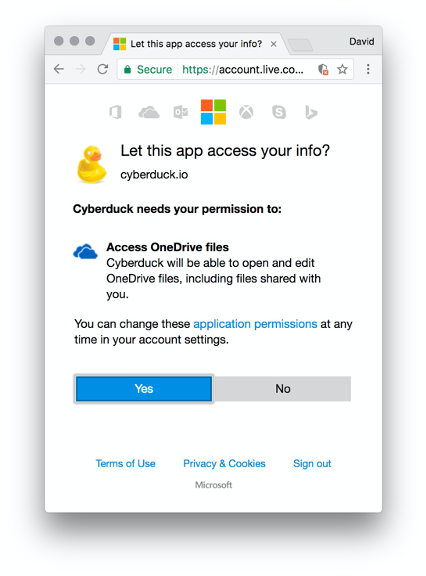
TrustedSec Practical OAuth Abuse for Offensive Operations – Part 1
Pawn Storm's Lack of Sophistication as a Strategy

OAuth, Breaking Cybersecurity News
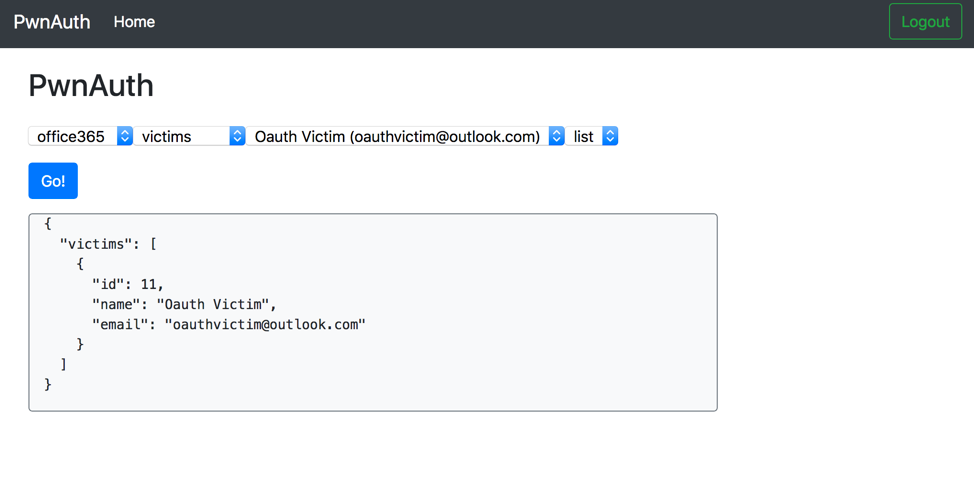
Shining a Light on OAuth Abuse with PwnAuth

OAuth, Breaking Cybersecurity News
APT28 Archives - Page 2 of 8 - Security Affairs

OAuth, Breaking Cybersecurity News
de
por adulto (o preço varia de acordo com o tamanho do grupo)


_(En,Ja,Fr,De,Es,It)-1472722018.jpg)

